City Hit by Cyber Attack: Was it the "Triple Threat," Inadequate Malware Protection, Human Error?
Posted June 11, 2019 01:00 pm
LAKE CITY, FL – Sometime over the weekend the city government of Lake City, Florida was hit with a virus-malware attack that the IT department claimed was the "Triple Threat." The third leg of the "Triple Threat" is a request for ransom. As of 9:20 am Monday, the City Manager said the City has not been asked for a ransom and so far he has not said it has.
Background
Related articles:
•
City Manager Declares War on Cyber Attacks –
Fortifying City IT: It Will Be Expensive
August 5, 2019
•
Lake City Finally Admits to Cyber Ransom, FL
League of Cities to Pay Approx $474,000
June 25, 2019
•
City Hit by Cyber Attack:
Was it the "Triple Threat," Inadequate Malware
Protection, Human Error? (June 11,
2019)
At 4:45 pm yesterday, June 10, Lake City City Manager Joe Helfenberger called the Observer to explain the City government had been hit with a cyber attack and that a press release would be forthcoming. While the Observer never received the press release, a lot of other media outlets did and reported verbatim that the City had been hit with the "Triple Threat" ransomware attack.
According to the conversation with City Manager Helfenberger, the attack came "sometime over the weekend."
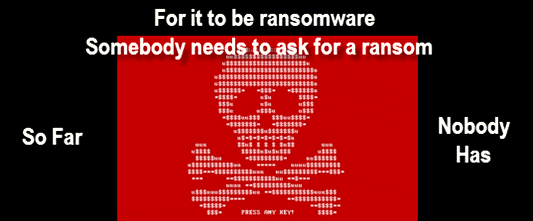
Mr. Helfenberger called the attack "ransomware."
Your reporter asked, "Has anybody asked you for money?"
Mr. Helfenberger answered, "Not yet."
Mr. Helfenberger said that the backup systems were deleted and all the City's servers were affected except for those of the airport and the police department. "They were on separate systems," he said, adding that some of the City's software is protected by third party vendors and those weren't affected.
Mr. Helfenberger said that the utilities system was "fine" and the "financial and payroll was not affected, but everything else was."
Your reported asked, "Do you believe it was ransomware?"
Mr. Helfenberger replied, "The IT people believe that."
The press release, posted to Facebook at 5:32 pm Monday, stated: "On Monday, June 10th, 2019, the City of Lake City was targeted by a malware attack known as the "Triple Threat."
The Triple Threat: Really?
The Triple Threat malware campaign combines Emotet, TrickBot and Ryuk malware.
"The first phase of the malware campaign begins with a phishing email, in which a weaponized Microsoft Office document containing malicious macro-based code is delivered to the user. Once the user opens the document, the malicious file runs and executes a PowerShell command.
The PowerShell command then attempts to download the Emotet payload from different malicious domains.
Once the Emotet payload executes, it continues infecting and gathering information on the affected machine, Cybereason researchers explained in a blog post."
The final phase is the ransomware (Ryuk). So far, the City has not had a ransomware demand.
At the end of last year Ryuk ransomware posed a growing threat to enterprises.
In the wake of the Ryuk ransomware attack on the Tribune Publishing Company last month [December 2018], security researchers are warning the threat to enterprises may be growing.
CrowdStrike in Sunnyvale, Calif., reported that Ryuk ransomware has accumulated more than $3.7 million in cryptocurrency payments since it first appeared in August. The research also noted that Ryuk has been used exclusively by a cybercrime threat group known as Grim Spider to target enterprises rather than individual users.
So Far, Nothing New From Lake City
Since at least the beginning of the year Lake City has had issues with its IT department. The City website has been wholly inadequate since the beginning of the year and the IT folks have yet to add information regarding who the City Council members are and their contact information. It took almost six months for the City to add events to its calendar before the event, rather than after.
Malware and viruses can enter the system through unprotected or inadequately protected portals or just plain human error.
What is human error? Someone clicks on an attachment from an unknown source and wham – the system is compromised.
Many firms, through their IT departments, send bogus emails to their employees to see who opens them. That is all their employees and they publish the results.
This has been found to inhibit the willy-nilly opening of unknown email attachments.
Epilogue
At publication time the City has not advised the Observer of any requests for ransom.
So far, the triple threat looks like a simple "person or people" error which got the system infected and took most of the City's system down.
Recovery time is unknown.